Customers expect a streamlined and easy online user experience. A little friction is okay — most people don’t object to typing in their password every once in a while. But when companies start layering on security steps like one-time passwords and security questions, customers can get frustrated quickly.
by Tiffany Mark
Strong online security is important, especially with sophisticated attacks on the rise. But it shouldn’t come at the cost of user experience. To protect users’ accounts and data without relationship-damaging levels of friction, you need to learn how to trust your users. That doesn’t mean having blind faith that every user is legitimate, but it does mean making creative use of technology to validate users.
Getting to know your good users better
It can be hard to know how to verify users online. But your customers already provide a lot of information you can use to understand who they are — you just might not be tracking it yet. Every human being has unique habits and traits that show up in the way they interact with technology. These fall into a few categories:
- Passive actions, like their typing cadence or way of holding their device (passive biometrics)
- Device information, like what type of device and software they use or what device settings they have
- Behaviors extracted from the data collected above, like logging in habitually from a certain place, typing in a given way or performing habitual actions inside the account (behavioral analytics)
By combining this information you can create a more holistic picture of who a customer is. Then, you can use that understanding to validate their identity in the background, without adding unnecessary friction.
For example, before the pandemic, NuData analysts found that most users interacted regularly with two to three devices — a work computer, a home computer and a mobile device — in a few consistent locations. If a user logged in from a familiar location on a recognized device, a security model could flag the interaction as safe without the need for multi-factor authentication or other extra steps. Similarly, when a user changes devices and/or locations, your security model can still recognize their inherent behavior — like typing cadence or device movements — without friction.
How to adapt when your users change on you
It’s normal for users’ behaviors, actions and device information to change due to individual circumstances (like, in the event of a move or job change) or global events. For example, when pandemic restrictions closed schools, workplaces, and stores and halted travel in spring 2020, millions of users changed their behavior almost overnight. Now that pandemic restrictions have eased a bit, we’re in the midst of another change.
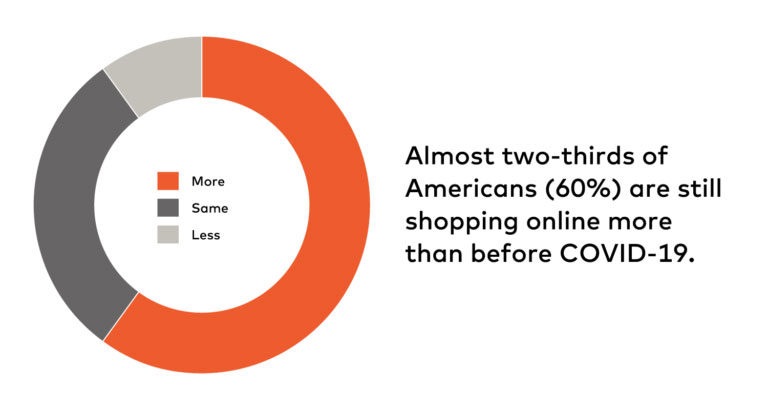
But companies shouldn’t expect everything to go back to the way it was before COVID-19. According to a PYMNTS research we commissioned, almost two-thirds of Americans (60%) are still shopping online more than before COVID-19. We can also see in our network that there are more IP addresses and devices associated with the average account than during the height of the pandemic.
Yes, it’s still possible to validate a user without friction even if they’ve abruptly changed their behavior. You need to look at the user holistically, as opposed to static data points. Problems — like a poor user experience or allowing fraudulent activity — arise when companies rely on only one data point to make decisions on whether a user is legitimate or not.
Be sure to look at the habits and traits we mentioned above, keeping in mind the broader context of their behavior. For example, right now companies can’t rely as heavily on device and location data to flag fraudsters, because fraudsters have gotten good at emulating the legitimate user. So just because someone logs into Ali’s account from his normal location, doesn’t necessarily mean it’s Ali. But other signals remain reliable, such as habitual actions like whether Ali is holding the device like he normally does or if he checks his balance before making a transaction to his cousin.
For example, a purchase or money transfer is more likely to be fraudulent if it involves an unusual sum of money for that user and comes at an odd time of day when they don’t habitually transact. The same is true for unusual purchases of big ticket items. By shifting which parameters you focus on to identify fraud — and evolving the rules along with your user’s patterns — you can keep up with their changing behavior while still keeping online friction to a minimum. The bottom line: Don’t ask your users to jump through more hoops if you can do it for them.
Friction is not a swear word
Streamlining your user experience doesn’t mean you can’t even dare to say the word friction. In fact, friction like requiring a CVC code or one-time password has its uses — specifically, stopping many bots and fraudsters in their tracks. Your goal should be to offer an experience that is as frictionless as possible and deploy step-ups intelligently where your security system identifies an interaction as high risk. The type of step up you use in a situation should depend on a couple factors:
- Type of threat. If a user displays telltale bot behavior, like attempting login with an incorrect password and username every few milliseconds, issuing a bot challenge like a CAPTCHA is likely to block the attack because (a) either the script won’t be able solve the challenge, or (b) it will be able to solve it, but displays bot-like behavior that a behavioral tool will be able to flag and stop in real time.By contrast, if the user behaves like a human, but types with a different cadence than the person associated with that account, requiring them to input a one-time password or a simple physical biometric request can confirm whether they’re legitimate or not.
- Riskiness of action. Customers are more forgiving of friction on transactions with high stakes, like opening a new line of credit or transferring a large amount of money from an account. In these cases, many customers see it as reasonable to request a copy of the user’s ID or other official verification if there’s any suspicion of fraud. On the other hand, requiring that level of verification on a low-cost purchase from a retailer would be overkill — and a potential source of frustration for customers.
Online identity is part of our identity
As more of our lives shift online, our online identities are becoming as rich and complex as our real-life identities. Security systems have to adapt to this new reality, while continuing to support a seamless online user experience. By looking at diverse data points to validate users, then adjusting friction according to type of threat and risk level, companies can build a more streamlined and secure online ecosystem.
This article originally appeared in NuData Security. Photo by Aziz Acharki on Unsplash.












2 comments